This year the M2M (Machine to Machine) market has exploded with the introduction for various low-power systems, and this includes Taggle Systems’ “Taggle” technology – a low-power, wide-area (LWPA) radio network technology which offers low-cost, power-efficient machine-to-machine communications for embedded systems across a very long range, for many kinds of sensors and applications in different sectors such as utility management and agriculture.
The team behind Taggle identified a gap in the M2M connectivity market which was not being addressed by existing, popular wireless connectivity technologies such as 802.15.4 and WiFi, which is low-power, wide-area networking with small amounts of data, with low bandwidth at a low cost, with minimal deployment of expensive infrastructure.
In many situations it is advantageous to send small amounts of data from field sensors over long distances, and Taggle’s energy-efficient, long-range wireless connectivity operating in the 900 MHz ISM spectrum helps to achieve this.
Today, Taggle is deploying its network of transmitters and receivers all over the country, becoming Australia’s first dedicated M2M network. Using their new technology, Taggle is deploying Australia’s only dedicated machine-to-machine telemetry network, enabling the cost-effective collection of data from thousands of Taggle-enabled devices in networks up to the scale of entire cities.
The Taggle network is made up of both transmitters and base station receivers. Taggle transmitters are commonly integrated into sensor or control devices in the field. For example, Taggle’s Automated Meter Reading (AMR) systems can be retrofitted to common water meters to read water consumption and broadcast the data back at one-hour intervals, for use by the water utility, local government and the individual consumer.
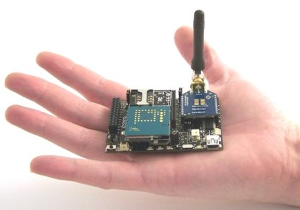
These AMR assemblies for water meters are a typical example of a device built around a Taggle transmitter. The transmitter offers low cost and strong energy efficiency, with the ability to transmit a small data packet once per hour for over ten years without replacement of its internal lithium battery.
Each transmitter module is equipped with four general-purpose I/O ports, making it possible to adapt to different kinds of sensors and applications. These sensor network “tags” are very compact and lightweight, and are able to tolerate the environmental conditions found outdoors in most field installations.
Each base station receiver is able to concurrently process hourly data from thousands of Taggle devices. The high receiver sensitivity of -130dBm means that each base station can receive data from tags up to several kilometres away, depending on local conditions. This strong link budget helps to reduce the number of base stations needed for Taggle connectivity across a wide geographic area, keeping the total system cost to a minimum.
With an initial focus on utility-scale Automatic Meter Reading (AMR) networks for water distribution, Taggle technology is already being used by a number of local councils and water utilities across Australia to gather water use data – which is not only useful for billing but also for leak detection, demand management, network optimisation and planning for future growth. It provides very fine-grained water use data on an hourly basis, as well as removing the need to manually take meter readings.
 Taggle’s network offers two major areas of use. The first is data acquisition, where small amounts of data can be collected from a very large number of sensors across a wide geographical area. The second valuable use-case is the location of objects within the area covered by the Taggle network.
Taggle’s network offers two major areas of use. The first is data acquisition, where small amounts of data can be collected from a very large number of sensors across a wide geographical area. The second valuable use-case is the location of objects within the area covered by the Taggle network.
Data can be collected from all sorts of sensors and devices and transmitted back to the Taggle network. Taggle’s wireless data acquisition hardware can collect data from electricity, gas and flow meters, rain gauges, and a range of other sensors such as pressure monitoring, sewer overflow, temperature, humidity or soil moisture sensors.
Once data has been collected it is processed by Taggle to produce data feeds for end users. These data feeds, which can be formatted to help meet individual users’ requirements, can be sent by email, secure FTP or web services to be integrated with the users’ chosen database or software interface.
Taggle’s radio network is also very cost effective for the sub-metering of utilities in large buildings such as high-rise apartments. Taggle technology allows a water meter, for example, to be installed for each individual user at low cost, allowing for individual billing. With all the data transmitted wirelessly back to the receiver, there is no need for labour-intensive meter reading.
In areas covered by three or more Taggle receivers, the locations of items fitted with Taggle transmitters can also be triangulated to within a few meters. With each Taggle receiver able to handle communications with thousands of tags concurrently, over distances of kilometres – this application of Taggle’s sensor network technology is very attractive in areas such as monitoring the movement of livestock, high-value goods in warehouses and more.
Here at the LX Group we have end-to-end experience and demonstrated results in the entire process of IoT product development, and we’re ready to help bring your existing or new product ideas to life. Getting started is easy – click here to contact us, telephone 1800 810 124, or just keep in the loop by connecting here.
LX is an award-winning electronics design company based in Sydney, Australia. LX services include full turnkey design, electronics, hardware, software and firmware design. LX specialises in IoT embedded systems and wireless technologies design.
Published by LX Pty Ltd for itself and the LX Group of companies, including LX Design House, LX Solutions and LX Consulting, LX Innovations.

 ery is supported using the CoRE Link Format standard, making the discovery of new resources on the network relatively easy. Related resources are grouped together into Objects, and this helps to cut down on processing overhead as the M2M client and the server on the platform side have a common understanding of what a certain resource actually is, by understanding the properties of an object that it is a part of – for example the manufacturer’s name, the type of network the device is currently connected to, the signal strengths of the cellular connection it uses, or other relevant properties.
ery is supported using the CoRE Link Format standard, making the discovery of new resources on the network relatively easy. Related resources are grouped together into Objects, and this helps to cut down on processing overhead as the M2M client and the server on the platform side have a common understanding of what a certain resource actually is, by understanding the properties of an object that it is a part of – for example the manufacturer’s name, the type of network the device is currently connected to, the signal strengths of the cellular connection it uses, or other relevant properties.